Where We Are
From workflows to a platform
Navi Today
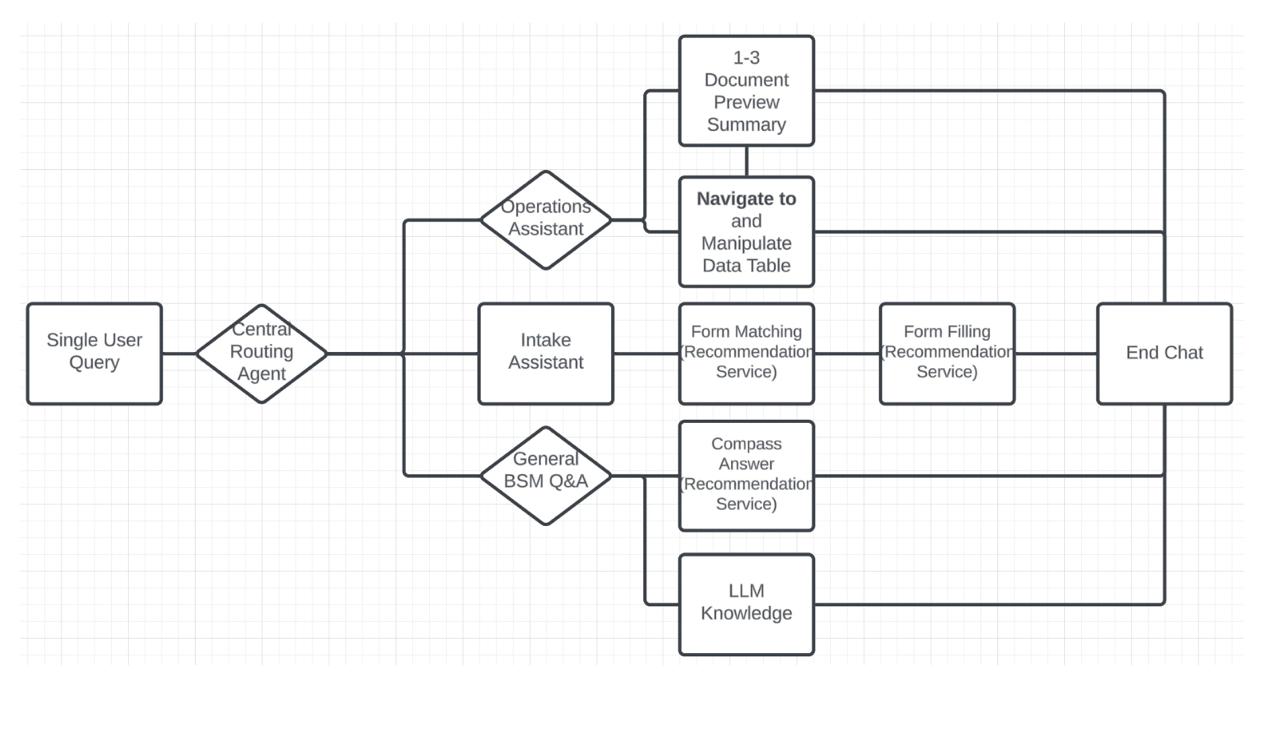
Target Architecture
Cloud Security Model
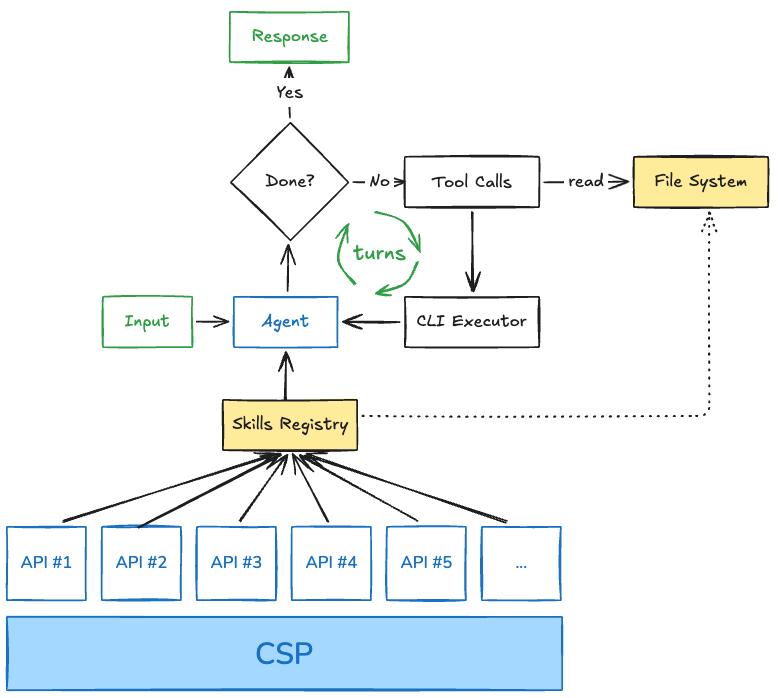
The architecture in one picture
The isolation boundary keeps suppliers apart. The gateway keeps credentials out of the model's hands. Logging happens at both layers.
2 / 4Design Philosophy
Infrastructure, not prompts
Tenant isolation must be enforced at the infrastructure layer. The model cannot be trusted to respect boundaries via prompt instructions alone.
Tenant identity bound at authentication
Supplier A's agent physically cannot reach Supplier B's data
Credentials never touch the model
Gateway injects auth into outbound requests — the agent generates intent, not credentials
Every action logged and replayable
Immutable audit trail — "the AI did something" is never an acceptable explanation
This aligns with Anthropic's secure deployment model, OWASP LLM06 (complete mediation), and the pattern used by every major agent platform (Manus, Devin, Codex, E2B).
Next Steps
What we need from you
Isolation model
Your read on the right execution isolation pattern for Coupa — Lambda, Fargate, or direct Firecracker?
Existing infrastructure
API gateways, auth patterns, audit systems we can build on rather than building from scratch.
Compliance path
What the Architecture Steering Committee needs to see to greenlight a system with model-driven autonomy.
AWS introductions
Solutions architects who specialize in multi-tenant agent runtimes and Firecracker-based isolation.
Your involvement
Advisory, co-design, or hands-on? We want to match your preferred level of engagement as we move from alignment to action.